Satellite Hacking: A Closer Look to the Sky
Satellites are vital to sustaining the current balance in the global economy, society, and advanced militaries. As such, states are increasingly recognizing satellites as critical infrastructure. They provide a significant role in climate and natural disaster monitoring, communication, early warning systems, global broadcasting, meteorology, navigation, precision strikes, reconnaissance, remote sensing, surveillance, and the advancement of science and understanding.
1. Introduction
A significant disruption to satellite services would have damaging effects on society. Limiting the information given might be due to security concerns or a lack of attention span on the part of its intended audience; however oversimplification gives the impression that an individual hacker sitting at their computer can access satellites with a few simple keystrokes. Conversely, it might lead others to dismiss the topic as fiction when there is a credible threat that needs to be addressed.
This article investigates key questions relevant to the topic of satellite hacking: What is the structure of satellite systems? What does it mean to ‘hack’ a satellite? And why are these systems vulnerable to hacking?
2. The Structure of Satellite Systems
In order to better address satellite hacking, it is first necessary to have an understanding of how satellites work. Most satellite systems conform to a broad template, which consists of the satellite itself, a tracking, telemetry, and control (TT&C) ground station, communications ground stations, and uplinks and downlinks between these ground stations and the satellite.
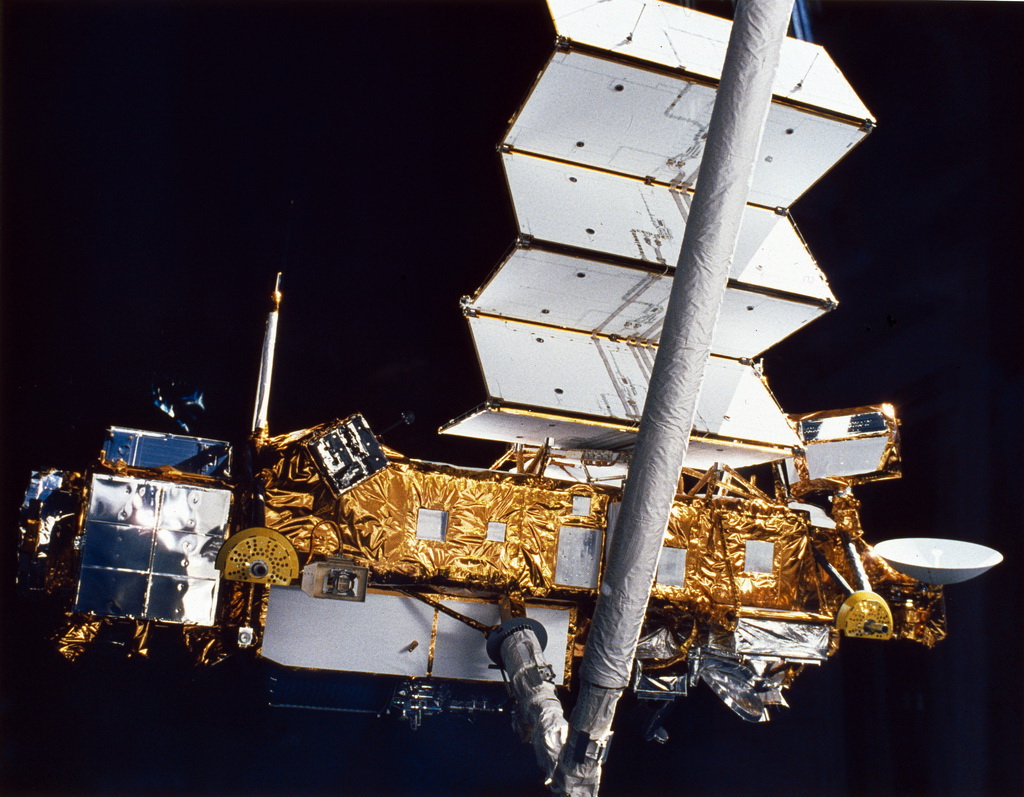
The satellite itself is composed of a bus and payload. The payload is usually a collection of electronic devices specific to that satellite’s desired function. For example, a surveillance satellite would contain imaging equipment, while the payload for a communications satellite would include transponders for receiving and relaying signals such as telephone or television. The bus is the platform housing the payload; this includes equipment for manoeuvring, power, thermal regulation, and command and control.
TT&C ground stations “perform tracking and control functions to ensure that satellites remain in the proper orbit and to monitor their performance. Communications ground stations process imagery, voice, or other data and provide, in many cases, a link to ground-based terrestrial network interconnections”. These ground-based terrestrial network interconnections communicate to and from the communications ground station but not directly to the satellite.
3. About Principal Threats
In a recent presentation, a popular IT security expert listed the following top 10 threats:
(1) Tracking – tracking over web data and software
(2) Listening – listening with the right equipment, frequencies, and locations
(3) Interacting – protocols and authentication used, radio transmissions need official license!
(4) Using – take over a bird or a TT&C
(5) Scanning/attacking – anonymous proof of concept in 2010 by Leonardo Nve Egea, scanning, DoS, and spoofing possible
(6) Breaking – old technologies used (X.25, GRE)
(7) Jamming – jamming well-known frequencies for satellites
(8) Mispositioning/Control – transponder spoofing, direct commanding, command reply, insertion after confirmation but prior to execution
(9) Grilling – activating all solar panels when exposed to sun, overcharging energy system
(10) Collisioning
4. Jamming
Jamming is probably the best-known satellite hacking technique; the attacker floods or overpowers a signal, a transmitter, or a receiver, interfering with legitimate transmission.
Interference has become the primary cause of the impairment and degradation of satellite services. The hackers use a directed antenna to produce the interference, usually a specifically crafted signal having enough power to override the original transmitted signal. Satellite jamming is a hacking method often used to interfere with communication for distribution of media for censorship purpose. The two forms of satellite jamming are “orbital” and “terrestrial”:
5. Eavesdropping
Differently from jamming, eavesdropping on a transmission allows an attacker to access transmitted data.
Despite the fact that almost every satellite communication is encrypted, it is quite easy to read posts on the internet that describe how to use off-the-shelf products to intercept satellite transmissions whether they carry satellite broadcast media, satellite telephone conversations, or Internet traffic.
6. Hijacking/Control
Hijacking is the unauthorized use of a satellite for transmission, or seizing control of a signal, such as a broadcast, and replacing it with another. The data transmitted could be acquired (eavesdropping) by attackers who could also modify it in transit (spoofing).
The term “Control” refers to the capability of a hacker to gain the control of part or all of the satellite architecture (ground station, bus, payload); particularly interesting is the hacker’s capability to maneuver the satellite in orbit.
Satellite hijacking is the illegal use of the satellite to transmit the attacker’s signal, which could override or modify legitimate transmitted data. Attacks against Internet data connections and media broadcasts are very common.
7. Scanning / Attacking
When explaining scanning and attacking concepts, it is useful to remember the content of a presentation made in 2010 by Spanish cyber security researcher Leonardo Nve at the Black Hat security conference in Arlington. The expert exposed to the audience a variety of tricks to access to satellite Internet connections and exploit them.
8. Conclusion
Satellite systems conform to a general template composed of TT&C and communication ground stations, uplinks and downlinks from these ground stations, and the satellites in orbit. Communication ground stations further link into extensive and varied networks of terrestrial interconnections. VSATs make up a large portion of these ground stations, and a wide range of user terminals are capable of receiving data downlinks. Distinction between four types of satellite hacking have been put forward – Jam, Eavesdrop, Hijack, and Control – and timelines of known incidents provided. Most of these satellite operators wish to keep information about their systems secret, which is a wise security precaution, but it makes analysis of them difficult. Further research could focus on a select sample of operators or satellite networks to limit the data being sought, and see if patterns emerge from that sampling.
9. References:
[1] Jason Fritz, SATELLITE HACKING: A Guide for the Perplexed, Culture Mandala: Bulletin of the Centre for East-West Cultural and Economic Studies, Vol. 10, No. 1, December 2012- May 2013, pp21-50.
Djekic M (2014-05-21 00:15:25). Satellite Hacking: A Closer Look to the Sky. Australian Science. Retrieved: Jun 05, 2026, from https://ozscience.com/technology/satellite-hacking-a-closer-look-to-the-sky/
 Follow
Follow